To play this video, enable Statistics cookies. Google/YouTube may process your data – Learn more.
Empowering federal agencies with innovative technology and professional services
CGI is a leading technology and professional services company that serves Federal agencies across defense, civilian, healthcare, justice, intelligence and international affairs. By integrating cutting-edge technologies with proven methodologies, CGI Federal ensures that our clients can confidently navigate their missions' complexities and achieve impactful, measurable results.
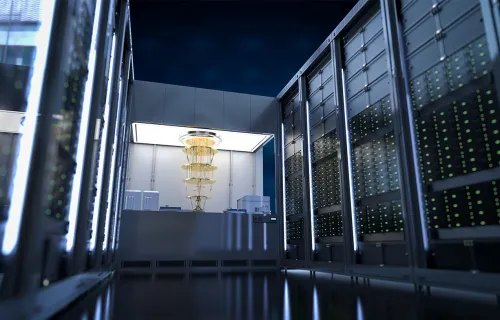
Maximizing efficiency with Momentum’s innovation and continuous compliance
CGI’s built-for-federal budget, financial and acquisition management solution, Momentum®, brings efficiency, increased productivity and cost reduction to the federal government through continuous innovation and centralized compliance updates.
Fostering communities and careers through U.S. onshore delivery centers
CGI's U.S. onshore delivery centers enable government agencies to diversify their IT sourcing models, reducing costs and risks with affordable managed services "made in America." This innovative approach has created over 1,000 quality jobs, generated millions of dollars in local economic activity, and established strong partnerships with communities, educational institutions, and government at all levels.
Perspectives

CGI careers
We are a global company of owners who shape the direction of our company and our own careers, while achieving meaningful results for our clients and making a positive impact on the communities we call home. Explore opportunities at CGI near your hometown or around the country.