As published in the new CGI-Governing Institute “Guide to Cybersecurity as Risk Management,” too often, a compliance-based approach to cybersecurity planning is unable to evolve with a public or private organization’s changing needs. A more effective alternative is a risk-based approach where organizations must understand their critical assets and the financial, reputational and regulatory risk should those assets be exposed.
In the private sector, organizations are embracing the NIST Cybersecurity Framework because of its provenance (the National Institute of Standards and Technology and industry collaboration) and its pragmatic approach to business-based risk management. The Framework was developed for the 16 critical infrastructure sectors in the U.S., but smaller and more diverse organizations also have found adoption value.
Corporations are also beginning to realize the risks associated with their third-party relationships and are evaluating the time and resources needed to demonstrate an effective third-party risk management program. The term “information value chain” makes a lot of sense and is being used to examine holistically, to the extent possible, the risks associated with information sharing among linked organizations.
Because information is now frequently dispersed to many outsourcing, hosting, cloud and other varied vendors and service providers, business leaders often are surprised to see the full list of entities that have access to, use or support their own organization’s information. Data flow diagrams often don’t tell the entire story of where information resides – some detective work within an organization’s information value chain likely is needed in most private and public organizations.
What follows are some key takeaways about cyber risk management from the CGI-Governing Institute guide, developed for elected officials, but relevant for many other executives.
Cybersecurity programs have grown exponentially due to the increasing complexity of threats to government operations. Funding continues to be a challenge, which is why prioritization and ongoing threat monitoring continue to be important parts of cybersecurity programs.
In the context of risk management, the cybersecurity effort is driven by business requirements. So, organizations must consider the financial risks, including cost of notification, potential sanctions and fines, and the impact of the loss of key operational information. They must also factor in the legal threats and the risks of reputation loss and loss of public trust.
Risk management-based cybersecurity is an ongoing process that must be re-evaluated constantly, with a feedback loop for adaptation and improvement. The model generally followed includes:
- Evaluate existing protection, plans, protocols and policies.
- Improve existing protection, plans, protocols and policies.
- Develop an environment that responds and adapts to the constantly changing threat environment.
- Re-evaluate constantly.
As part of the government’s traditional decision-making and budgeting framework, security threats are identified, assessed and prioritized, and budget resources are assigned accordingly to minimize the likelihood and impact of a breach. A risk-based management process will identify an organization’s most valuable assets and enable technology professionals, agency leaders, elected officials and fiscal staff to work together to determine funding priorities and strategies.
According to a survey of state government Chief Information Security Officers (CISOs) by the National Association of State CIOs (NASCIO), more funding was made available for cybersecurity programs in 2014 than in 2012. However, in what NASCIO describes as a “budget-strategy disconnect,” adequate funding continues to be a challenge. Integrating cybersecurity into the risk management process can help executives prepare a business case for cybersecurity in the budget processes.
How to gain budget funding for cybersecurity efforts is always a challenge – and this is why private sector organizations increasingly are examining the NIST Framework. Its components tell a compelling risk management story that can be used to illustrate both technology and behavioral requirements. It breaks down hundreds of controls into a common sense and meaningful approach to information security and privacy management into key functions: identify, protect, detect, respond and recover.
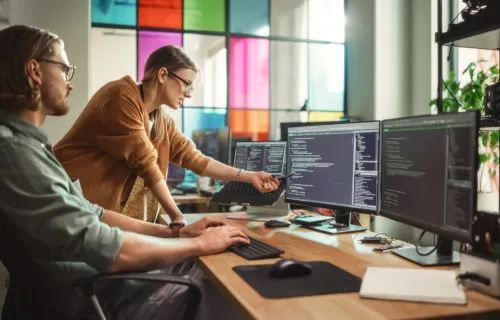
In the past, focus typically has been on technology-based evaluation, improvement, development and re-evaluation. Recent private sector and academic attention has been focused on the “people-centric” side of cyber risk and associated risk management efforts. This is because, while external threats exist, often is it a person’s behavior that allows the threats to get in. All organizations, public and private, are turning their attention to the “human versus human” context for managing information security risk. Insider threats, policy non-compliance, phishing and other social engineering exercises that target individuals are being considered from a behavioral perspective. Organizations are beginning to introduce new risk management behaviors by establishing security and privacy as part of organizational culture and establishing people-centric metrics and measurements of behavioral change.
These easily can be broken down into technology-based and behavioral-based activities to be budgeted within virtually any organization, and make it easier for CISOs and CEOs to collaborate about cybersecurity funding in understandable terms and, hopefully, with effective results.