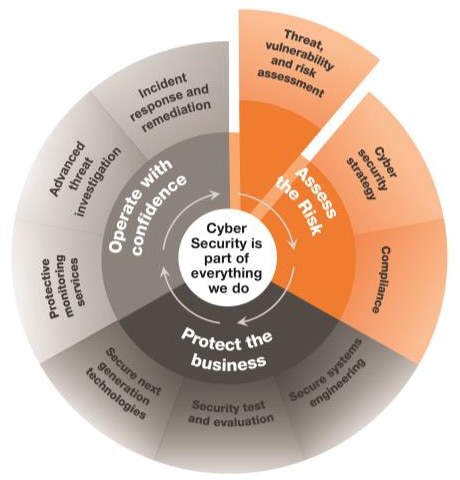
Organisations are increasingly dependent on information systems for all their business activities with customers, suppliers, partners and their employees. Organisations need to be confident that they can operate securely. Their cyber security risks need to be understood in the context of the overall business. For many years we have been supporting our clients to embed cyber security into their business operations.
Our Threat, Vulnerability and Risk Assessment Services
CGI’s vulnerability and risk assessment methodology provides accurate, controlled, repeatable, and in-depth findings and actionable, prioritised recommendations for remediation. It is customised to focus on a client’s requirements for evaluation, risk tolerance and specific business goals. Our skilled experts will assess the risks and identify vulnerabilities in the applications, systems and networks, providing cost-effective recommendations to manage them.
Our approach
The CGI methodology uses multiple automated assessment tools to target discovery, foot-printing and initial assessment.
STREAM is a risk management product that we have successfully used across multiple sectors. It is versatile and can be used with different profiles to meet the needs of individual clients. Its great strength is that it is designed to be an operational tool so, whereas other tools often take a snapshot of a security risk at that moment in time, STREAM can react immediately to any changes which are input during the assessment, either actual or potential to give an indication of the changing risk position.
Alternatively, our own IRIS methodology enables us to perform risk assessments quickly and cost-effectively. The outputs inform the client of their security risks and enable them to implement a coherent, comprehensive and cost-effective security regime combining risk analysis and business impact analysis together.
Our methodology includes a manual validation and testing phase that verifies the accuracy of each automatically detected vulnerability and includes tests that the automated tools are known to miss. It is performed in a carefully controlled manner with input from, and coordination with, the client at all phases. All test parameters are recorded to allow retesting under the same conditions. Raw data of test results is provided to the client so that each finding can be replicated and verified.