CGI has a 45-year heritage of helping clients reinvent and secure their businesses for the future through the delivery of innovative and advanced cybersecurity services in complex, environments across the globe, including the defense and intelligence sectors. We have invested heavily in establishing our credentials, working closely with international security associations and standards bodies.
While cyber threats are global, we know that requirements vary locally and challenges are unique to each organization.
Through our expert talent, deep technical and business knowledge, best practices and accelerator frameworks, we provide strategic advisory services, engineering of secure outcomes and managed security services. We work closely with you to ensure security controls are baked in, not bolted on.
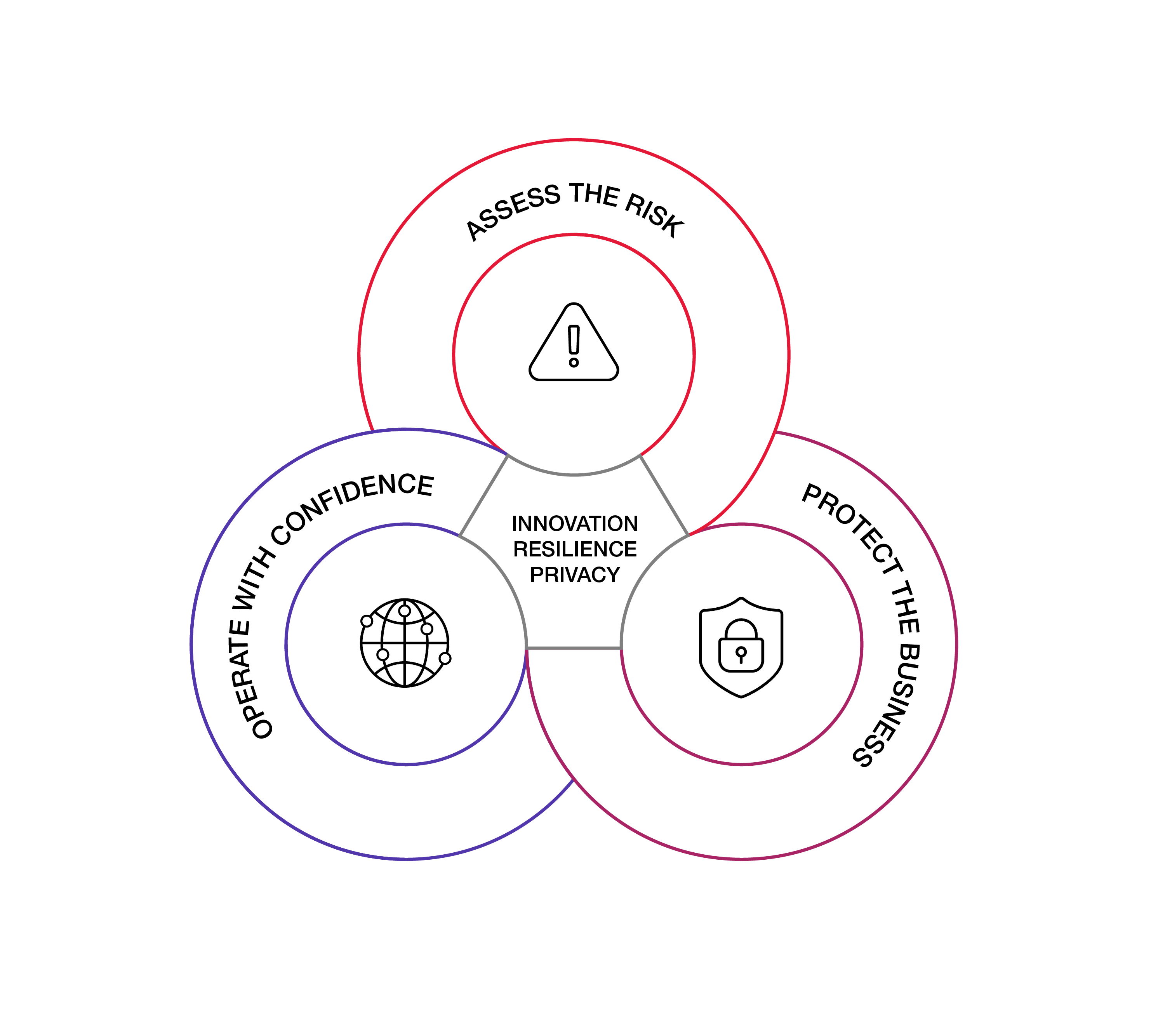
Assess the risk
Helping clients to assess and manage security vulnerabilities so they can be confident their organization is secure, compliant and ready to grow.
-
Threat & Risk Management
-
Governance, Management & Compliance
-
Security Strategy Maturity & Awareness
Protect the business
Helping clients to build in security early, and test its ongoing effectiveness- securing the systems an organization relies on to operate and grow.
-
Security Architecture & Engineering
-
Secure Engineering & Enabling Technologies
-
Testing & Assurance
Operate with confidence
Helping clients to monitor prevent and respond to security attacks in a reliable and cost effective way.
-
Incident Response & Forensics
-
Security Operations
-
Cyber Threat Intelligence